Access Control That Doesn't Get in the Way
Protect sensitive company data without slowing work down. Access and security scale naturally across roles, teams, and everyday workflows.

Protect sensitive company data without slowing work down. Access and security scale naturally across roles, teams, and everyday workflows.

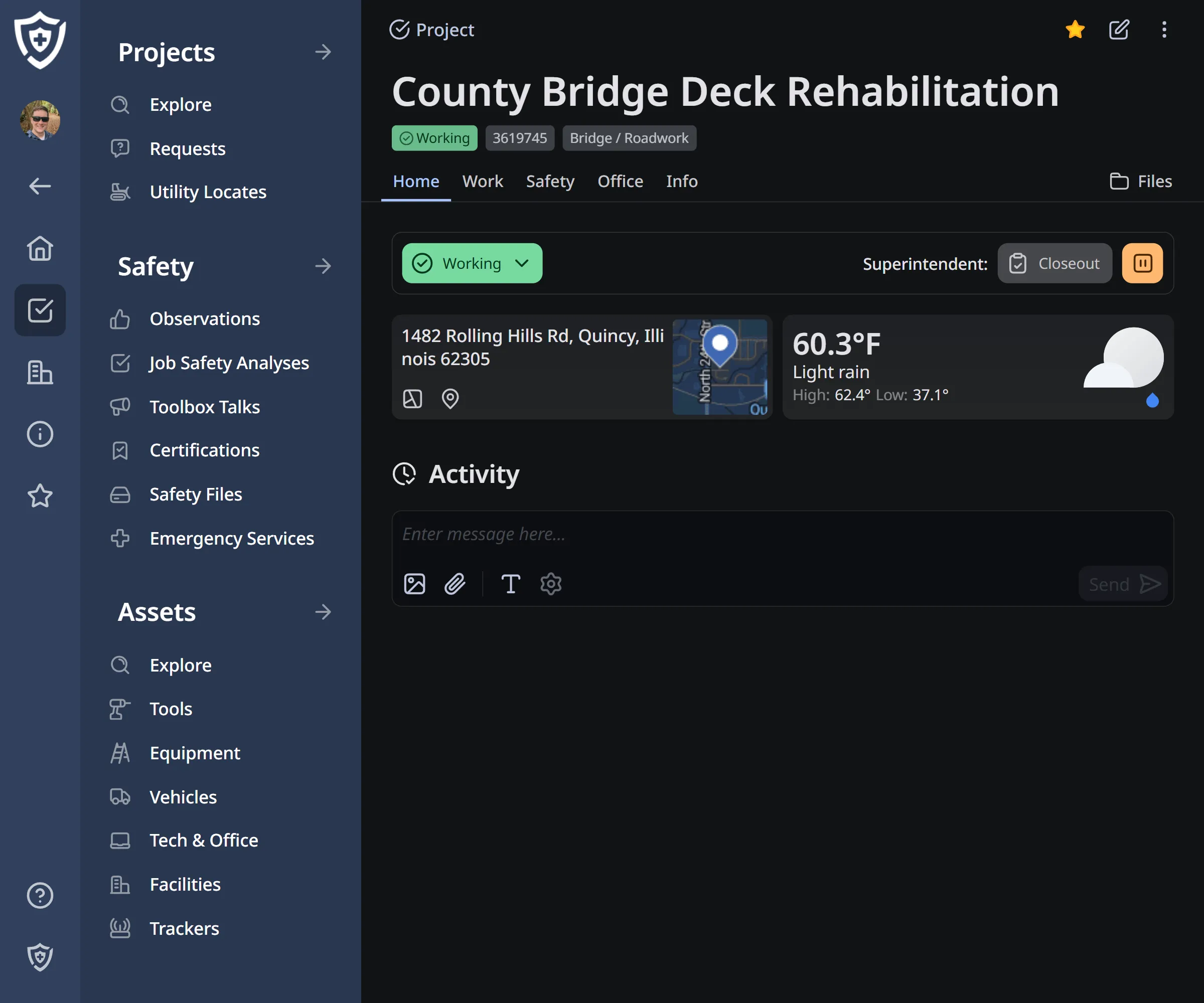
Permissions that match workflows
Access is tied to roles and responsibilities. Teams see what they need to see, can act where they're supposed to, and aren't blocked by unnecessary restrictions.
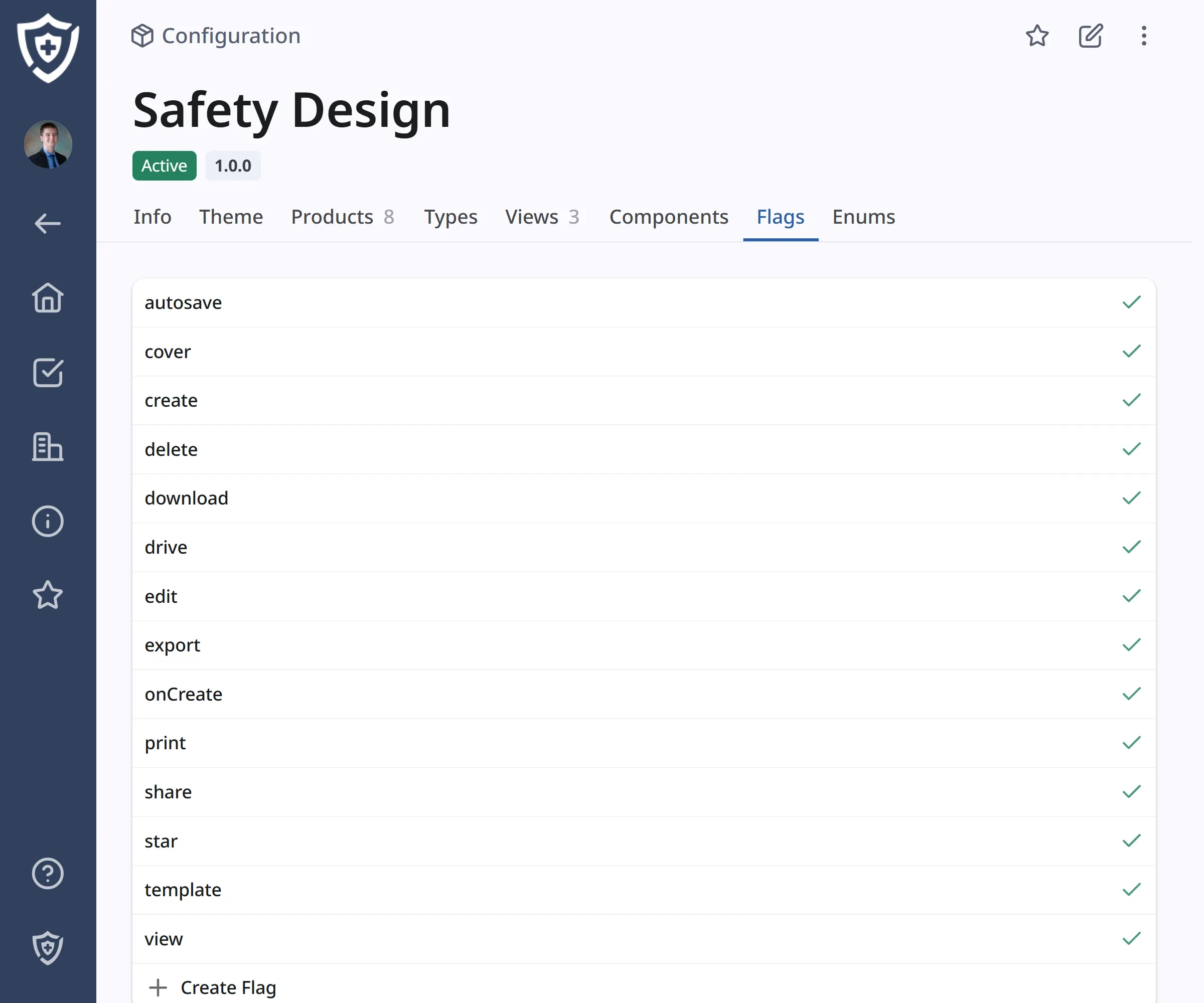
Flexible feature control
Set global flags that control access to app features depending on your desired config.
Security handled at the foundation
Data is encrypted in transit and at rest using modern, industry-standard practices. Protection is built in, with nothing extra to configure or manage.
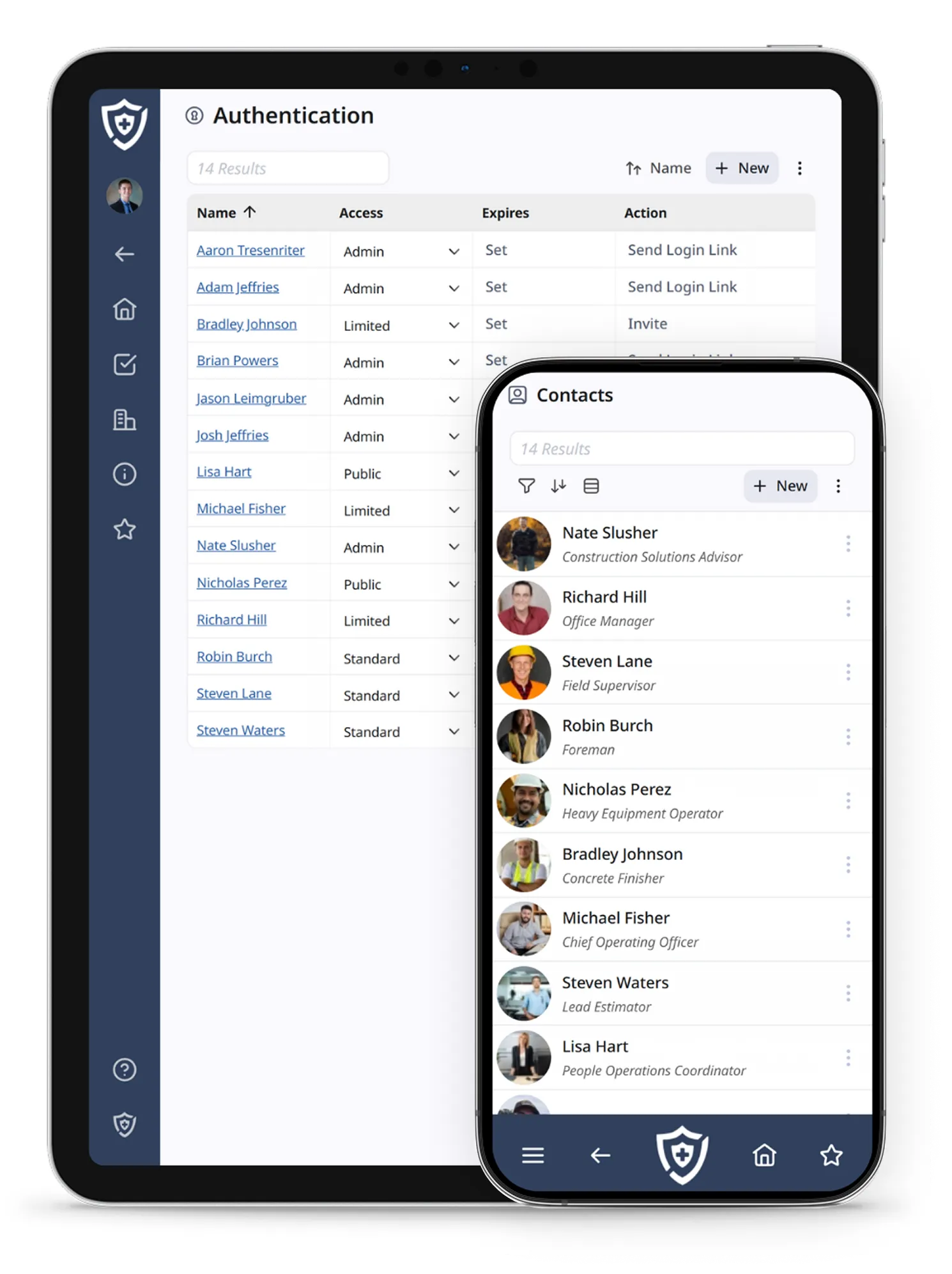
One place to manage people and access
Manage users, roles, permissions, and access changes from a single interface. As teams evolve, access stays accurate without manual cleanup.
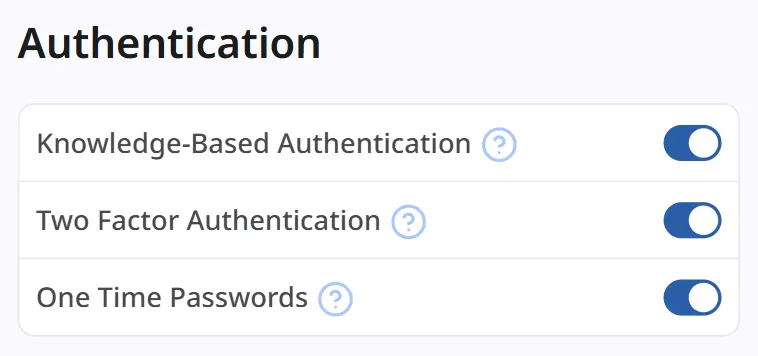
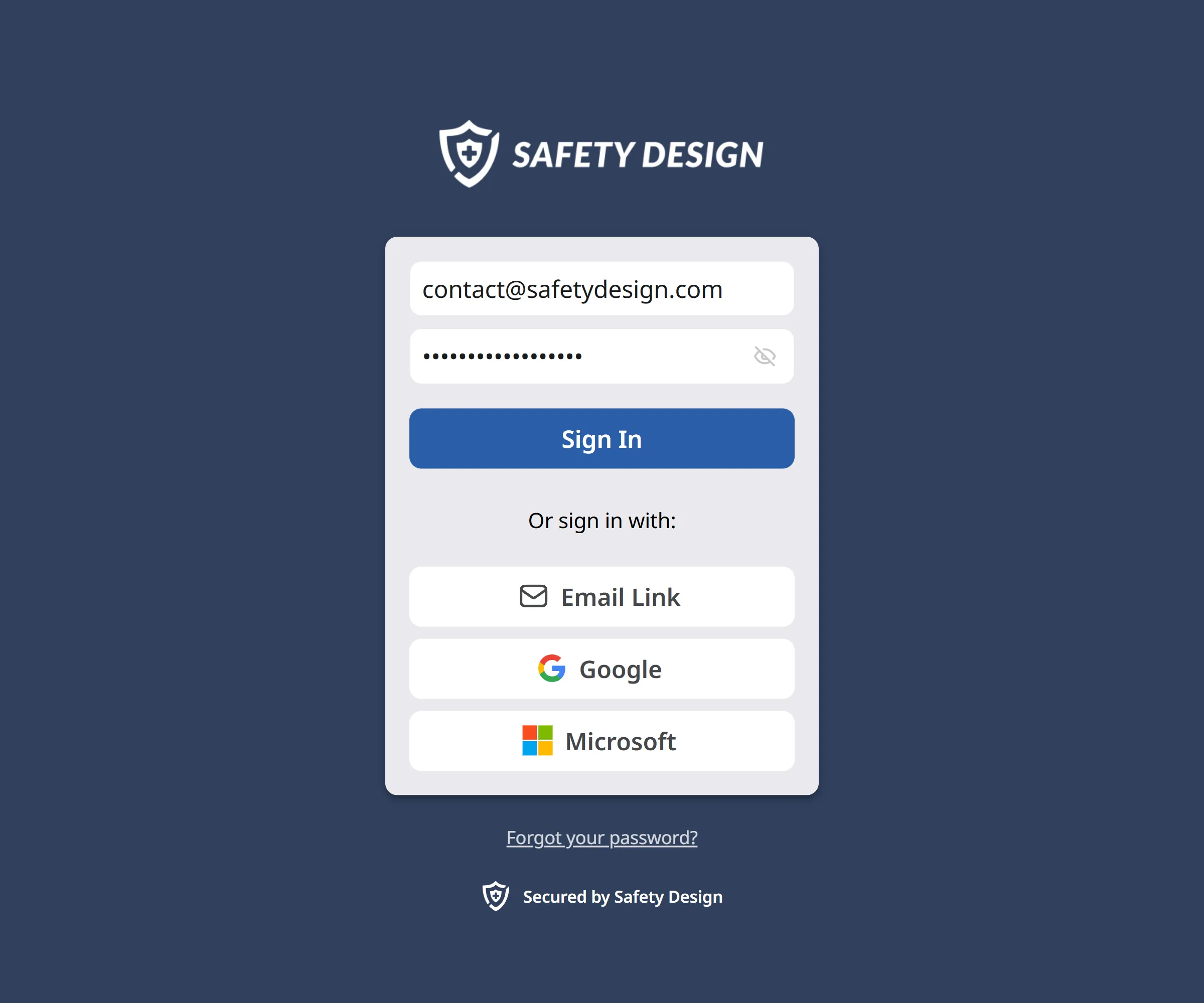
An extra check where it counts
Require a second verification step during login to reduce unauthorized access without making sign-ins a chore.
Password rules you control
Set and enforce password requirements that align with internal standards. Consistent rules help keep accounts protected by removing individual judgment.
Get started with a complementary Action Plan outlined by industry experts.